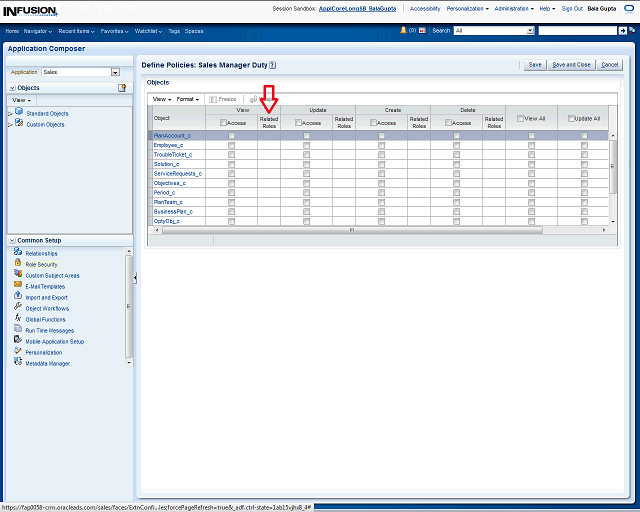
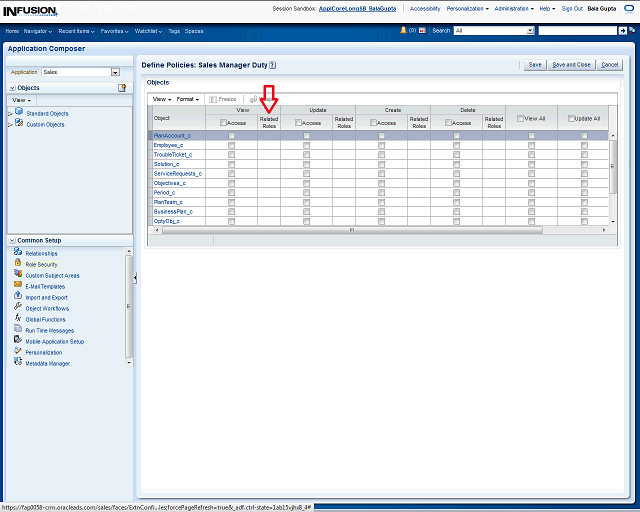
Defining security by role works the same way as by object. The only difference is the related roles column.
If you see a related role name in this column, this means that the role you are setting up inherits its access from the related role. You can drill down
into the related role to view its security policies.